He11singKG
New Around Here
Hello. I'm working with some asus routers, mostly model RT-ACRH13.
Firmware
3.0.0.4.380_8457
3.0.0.4.380_8347
3.0.0.4.380_8119
3.0.0.4.382_52134
3.0.0.4.382_52504 and some other
Have this setup
Firewall enabled
WAN Access disabled
SSh enabled with key autorization
PPTP disabled
OVPN enabled some udp/some tcp
For few months i have been getting this trouble
Can't connect to ovpn - port changed to udp 31194/60091, also router has newly generated certificates. In custom configuration there is such info
In init-start file this info
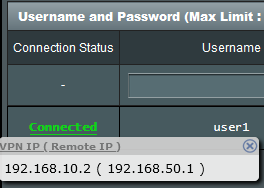
Pptp becomes enable and always there is such authorization pair - user1:admin123 with active connection from lan
I keep deleting the updater file and info from the init-start file, but after some time, they reappear, and the problem comes back.
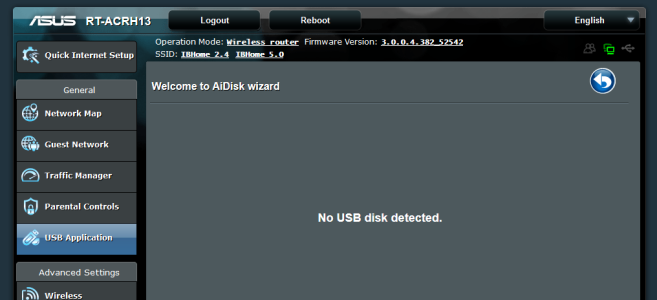
I've found that 443 port which associated with Aicloud is open, but I can't close it. In usb applications there is no options for aicloud.
I manually add this firewall rule iptables -D INPUT -p tcp --dport 443 -j ACCEPT it closes port for a few period but later port is opened again
I guess router is getting exploited via this port, but sometimes I don't have it opened and routers are still getting this problem.
I updating now to latest firmware 3.0.0.4.382_52542, hope it will help, but I still have 443 opened on most of devices. How can close it?
Firmware
3.0.0.4.380_8457
3.0.0.4.380_8347
3.0.0.4.380_8119
3.0.0.4.382_52134
3.0.0.4.382_52504 and some other
Have this setup
Firewall enabled
WAN Access disabled
SSh enabled with key autorization
PPTP disabled
OVPN enabled some udp/some tcp
For few months i have been getting this trouble
Can't connect to ovpn - port changed to udp 31194/60091, also router has newly generated certificates. In custom configuration there is such info
or thisup '/jffs/scripts/init-start';
/bin/sh /jffs/init_script
up "/bin/sh /jffs/updater"
In init-start file this info
Can't connect to ssh - port stays the same, but connection refused - after reboot it works againecho "*/1 * * * * /jffs/log/.hjmi -w -d -k telnet,dropbear,wget,openvpn -b http" > /jffs/log/$(nvram get http_username)
/usr/sbin/crond -c /jffs/log
Pptp becomes enable and always there is such authorization pair - user1:admin123 with active connection from lan
I keep deleting the updater file and info from the init-start file, but after some time, they reappear, and the problem comes back.
I've found that 443 port which associated with Aicloud is open, but I can't close it. In usb applications there is no options for aicloud.
I manually add this firewall rule iptables -D INPUT -p tcp --dport 443 -j ACCEPT it closes port for a few period but later port is opened again
I guess router is getting exploited via this port, but sometimes I don't have it opened and routers are still getting this problem.
I updating now to latest firmware 3.0.0.4.382_52542, hope it will help, but I still have 443 opened on most of devices. How can close it?